You probably thought you were done with the tests the minute you graduated college! But risk assessments, like a test for your bank’s security, will tell you something much more important than how well you know modern literature. Regular risk assessments are not just a regulatory requirement but also a critical component of a bank’s […]
Tag Archives: cybersecurity
In a world teeming with digital threats, the banking sector isn’t just a target; it’s the bullseye. Every advanced cyber maneuver calls for an equally precise and proactive defense. After all, the stakes are high—your customers’ financial security and trust are on the line. That’s why the Federal Financial Institutions Examination Council (FFIEC) developed its […]
Do you know how many of your employees would report it if they accidentally clicked a phishing link? Studies have found that 43% of employees don’t report incidents because they’re scared of the consequences, 36% assumed they didn’t need to report, and 32% of respondents simply forgot. How confident are you that your bank’s employees […]
The banking industry, revered for safeguarding critical financial data, has faced a barrage of cyber threats recently. These incidents, while alarming, help decision-makers like you identify emerging threats and stop them in their tracks. Let’s delve into the key takeaways from these events and explore actionable insights that banks can adopt to bolster their defenses. […]
Tens of billions of emails are sent every single day. Not all of them have that document you’ve been waiting weeks to receive. In fact, an estimated 3.4 billion emails are sent by cybercriminals every day. But how often are they being opened? Phishing attacks have an open rate between 17% and 53%, depending on […]
Cyber attacks are not slowing down. And with more and more people accessing company networks remotely, the problem is only getting worse. All it takes is one compromised credential or legacy application to cause a data breach. Now is the time to step up your security. Multi-Factor Authentication (MFA) is a security system that verifies […]
A recent study by a Security Awareness Training platform showed that the average rate at which employees of small banks clicked on phishing emails was 25% (the rate for bigger banks is even worse!). Ransomware (malware that encrypts your data and only provides a decryption key if you pay a ransom) continues to be a […]
What does it mean to be “threat ready” in an industry as sensitive as banking? The term is tossed around a lot. But what does that look like for your institution? In simple terms, being threat ready means having the right technology, trained staff, and proactive strategies in place to protect your bank’s assets from […]
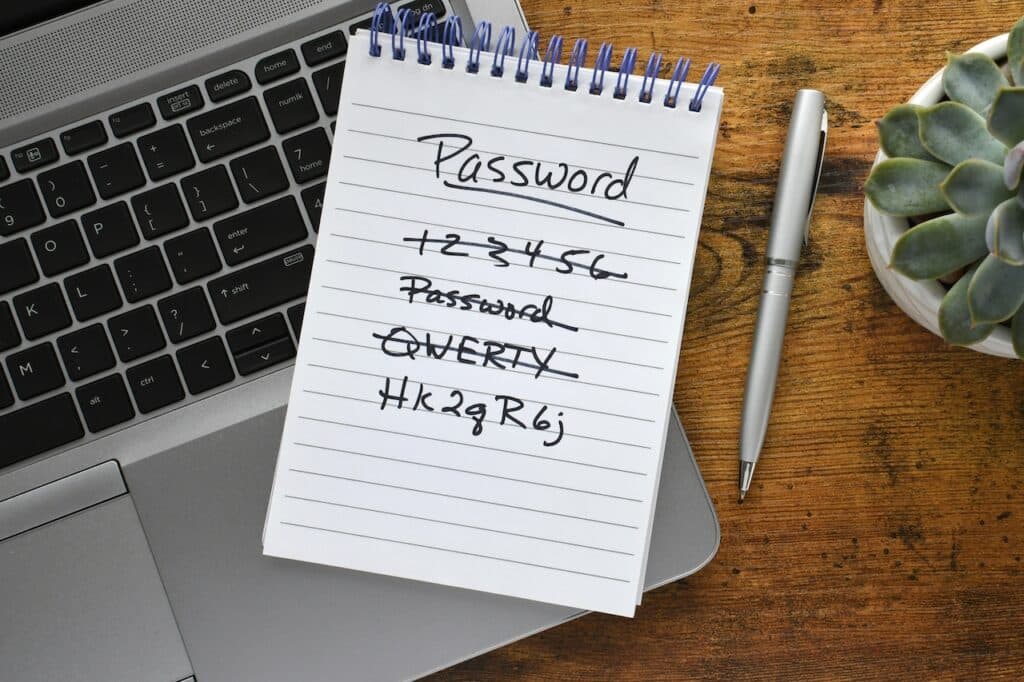
In March of 2022, TransUnion South Africa announced that their records had been breached—the group that took responsibility for the hack claimed that they stole 54 million records. They also claimed that the server they hacked was protected with the word “password.” It’s the oldest security joke in the book but if what the hacking […]
The hidden costs of a cyberattack are just that—hidden, below the surface, a ripple effect that can last for years to come. IT companies are quick to share stats about the average cost of a data breach (now at over $5 million) but what goes into those calculations? And is that just a loss of […]